Software and cybersecurity tool provider JKI has launched an automated security analysis platform for LabVIEW applications, giving test engineers a tool to identify software weaknesses and document dependencies against cybersecurity regulations.
The platform arrives as cybersecurity obligations expand across regulated industries.
In the USA, the National Institute of Standards and Technology (NIST) 800-53 framework requires static code analysis to identify common software flaws, and the Cybersecurity Maturity Model Certification program is introducing enforceable requirements for defense contractors.
In Europe, the Cyber Resilience Act (CRA) introduces vulnerability reporting obligations from September 11, 2026, with broader cybersecurity requirements following from December 2027.
While static application security testing (SAST) tools are well established for text-based programming languages, JKI said no equivalent had previously existed for LabVIEW, a visual programming environment widely used in aerospace and defense test systems.
Without such tooling, manual security reviews can be inconsistent and miss weaknesses specific to dataflow programming, the company said.
The JKI Security Suite includes a SAST tool that analyzes LabVIEW source code, classifies findings against the MITRE Common Weakness Enumeration (CWE) framework and provides remediation guidance.
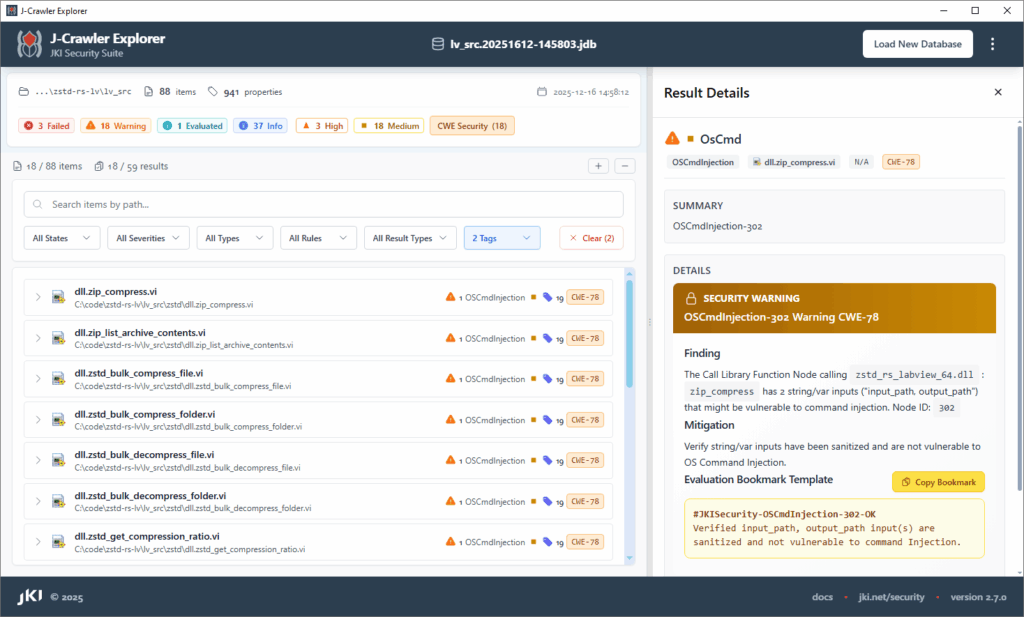
The suite also generates software bills of materials (SBOMs) to document dependencies including instrument drivers, third-party packages and open-source components, supporting vulnerability tracking through development and deployment.
A command-line interface allows scans to run inside continuous integration and continuous deployment (CI/CD) pipelines for automated security validation. The platform aligns with NIST, MITRE CWE, NASA software standards, the EU Cyber Resilience Act and ISO 9001, according to JKI.
For defense organizations, the absence of a static analysis tool for LabVIEW has the potential to jeopardize Authorization to Operate (ATO) status for classified work, the company said. Additionally, getting visibility into the software supply chain for LabVIEW applications (software dependencies in test frameworks, such as instrument drivers, third-party packages, and open source components) and tracking disclosed vulnerabilities for those components is also a complex and time-consuming manual process.
The JKI Security Suite has been developed to address these challenges by integrating automated security analysis into existing development workflows.
JKI is targeting the suite at aerospace test and validation platforms, automation systems and other high-reliability applications.
“Test teams are being forced to rethink their development workflows in response to growing security demands,” said Steve Summers, security lead at Emerson. “Because LabVIEW is central to how many of these teams operate, access to robust security tools is essential for developing and documenting secure, trustworthy code.”
The JKI Security Suite will be demonstrated at NI Connect 2026, running from May 12 to 14 at the Fort Worth Convention Center in Fort Worth, Texas.





